Authentication and user directory introduction
Installed clients, as well as web clients, connect to the Spotfire Server. When users of either client log in to a Spotfire Server, two things happen before they get access: authentication and authorization.
Authentication is the process of validating the identity of a user. After their identity is validated, the user is authorized in the user directory. Authorizing users determines their access rights within the Spotfire environment—in other words, what they are allowed to do.
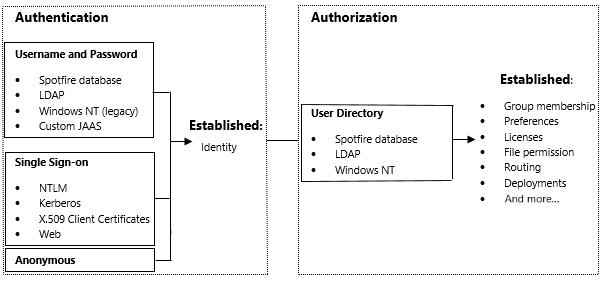
If username and password are used for authentication, users are checked against the internal Spotfire user directory, a custom Java Authentication and Authorization Service module, or—the most common option—an external LDAP directory. Spotfire has built-in support for Microsoft Active Directory and the Directory Server product family, which includes Oracle Directory Server, Sun Java Directory Server, and Sun ONE Directory Server. Other LDAP servers can also be used.
For single sign-on, Spotfire supports NTLM, Kerberos, X.509 Certificates, and web authentication.
For anonymous authentication, a preconfigured Spotfire user identity is used to authenticate with the Spotfire Server.
Regardless of how the user is authenticated, the process of authorization is the same. The server checks the Spotfire user directory to determine which licenses, preferences, and permissions have been set for the user.
Optionally, the user and group accounts in the Spotfire user directory can be synchronized with an external LDAP directory. Spotfire supports the same LDAP servers for directory synchronization as it does for authentication.
For more information, see User authentication.
- Spotfire Server introduction
- Spotfire database introduction
- Nodes and services introduction
- Spotfire clients introduction
- Environment communication introduction
- Users introduction
- Groups and licenses introduction
- Preferences introduction
- Deployment introduction
- Spotfire library introduction
- Routing introduction
- Data sources introduction
- Logging introduction
- Administration interface introduction
- Example scenario